The all-in-one open source security scanner
Trivy is the most popular open source security scanner, reliable, fast, and easy to use. Use Trivy to find vulnerabilities & IaC misconfigurations, SBOM discovery, Cloud scanning, Kubernetes security risks,and more.
Get TrivyComprehensive Coverage
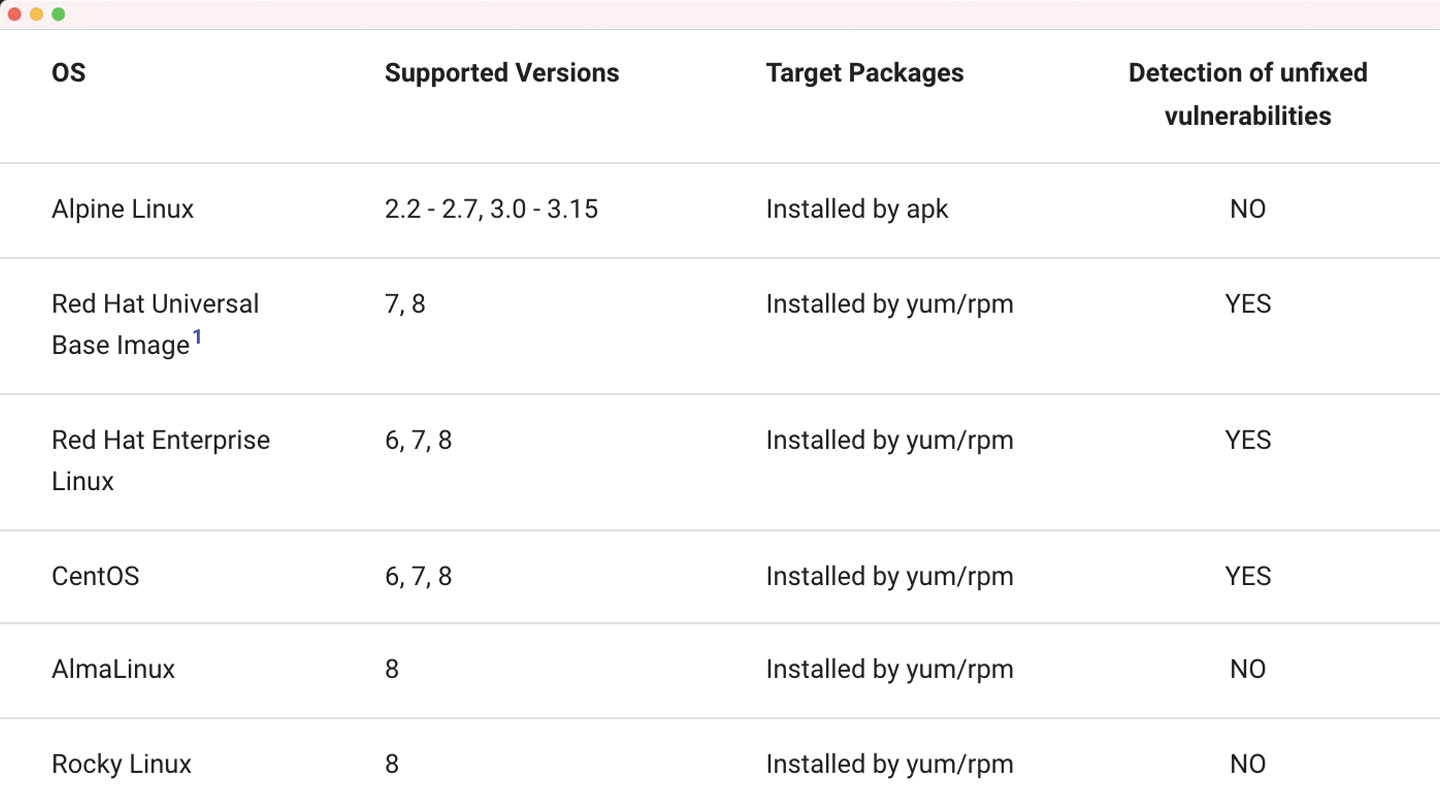
Trivy detects vulnerabilities from a wide array of operating systems and programming languages, across different versions, and vulnerability sources.
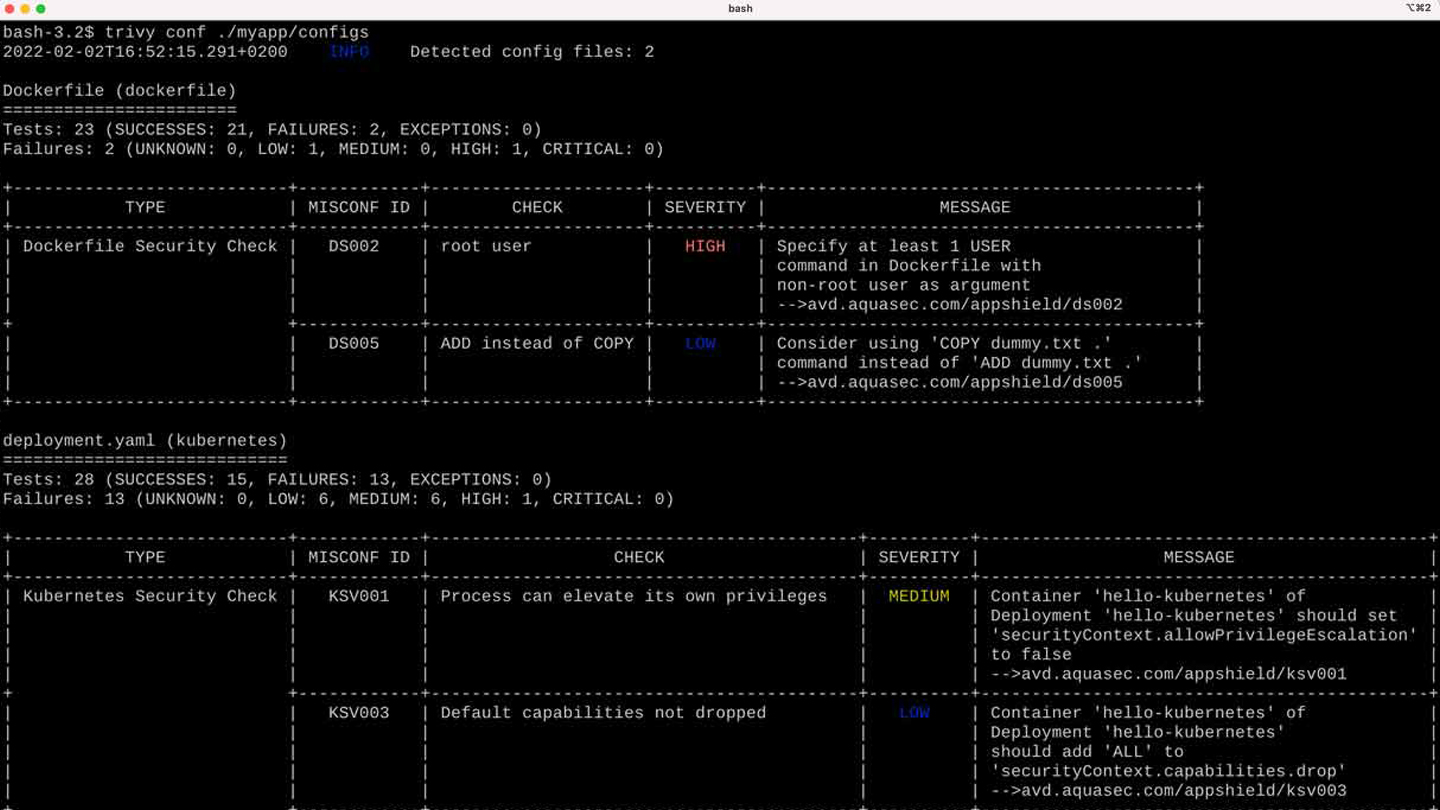
Infrastructure as Code scanning
Detect common misconfigurations with Trivy, using the same familiar tool and workflow that you already have in place for vulnerabilities. Trivy scans Terraform, CloudFormation, Docker, Kubernetes, and many other IaC configuration files for security issues right alongside vulnerabilities. Trivy IaC is brought to you by the team behind the popular tfsec project.
Easily run everywhere
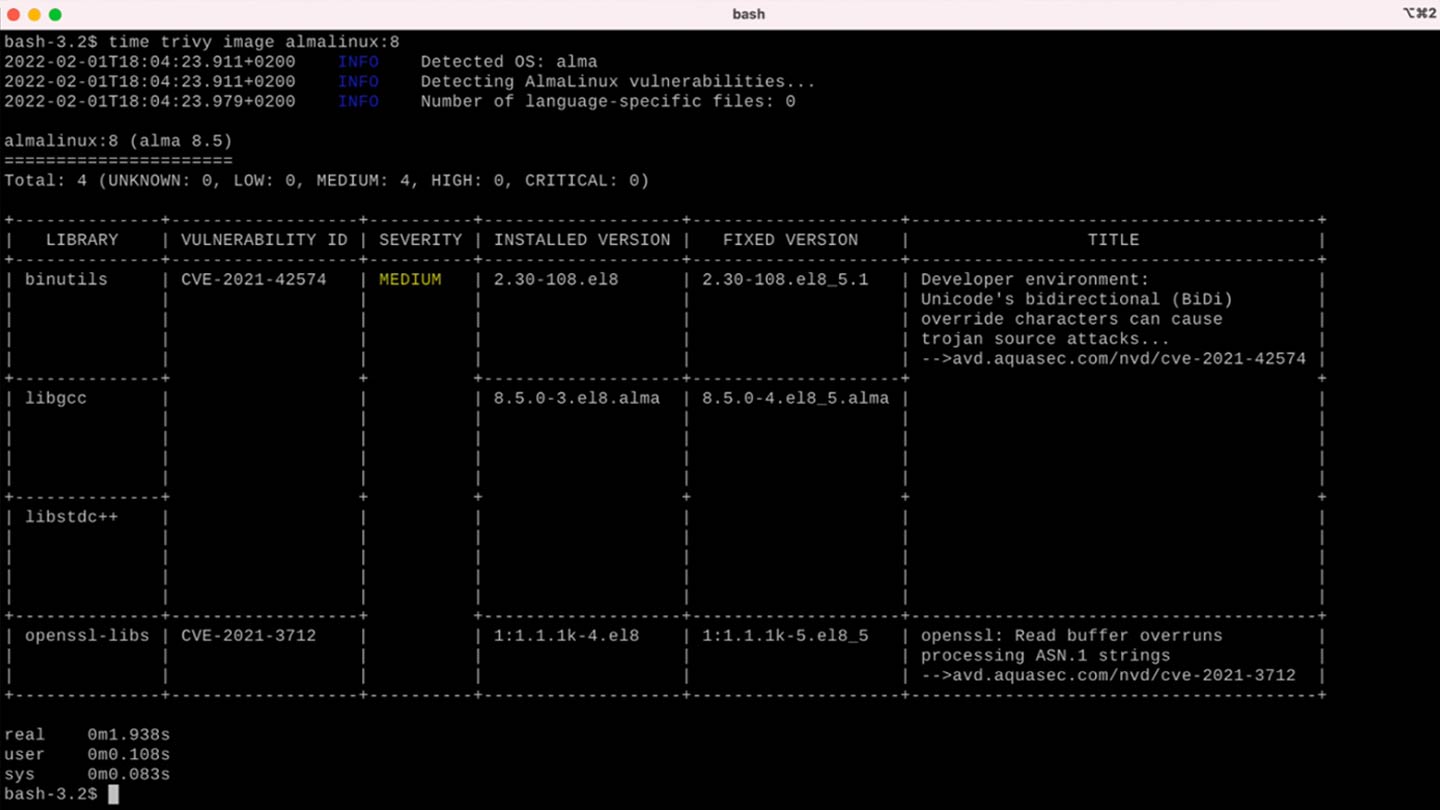
Trivy is a single binary with no dependencies! There’s no database to maintain, no external tools it relies on, no runtime requirements whatsoever. Every OS and CPU are supported, just download and run the binary, or find Trivy in your favorite package management tool. Cold run scans take seconds, and recurring runs are instantaneous.
Versatile to fit your needs
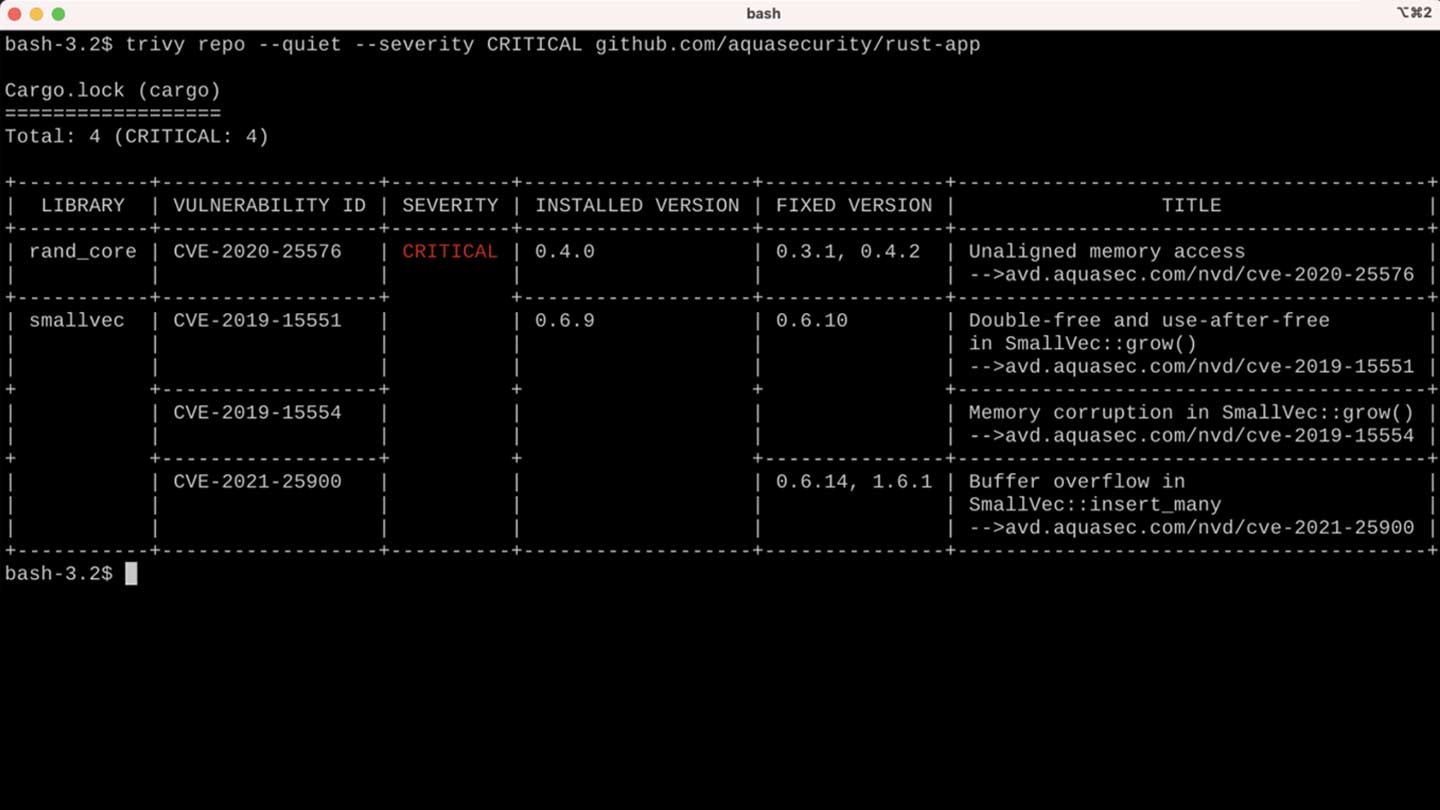
Trivy scans local and remote container images, supports multiple container engines, as well as archived and extracted images. It works on raw filesystem and remote git repositories. With Trivy, you can scan whenever and wherever you need to.
Truly Open Source
Licensed under the permissive Apache 2.0 software license, Trivy is totally free to use. Use it, fork it, spread it – we’re good with it. Industry leading vendors are using Trivy to power their services. How will you use Trivy?